Eliminate the
Browser Blind Spot
Keep Aware is the Human-centric Browser Security Platform. It provides robust protection against attacks including phishing, spoofing, social engineering, and malicious extensions.

Protecting the Browser:
A Top Priority for Security Leaders
“Even with the latest network and email security solutions in place, user-facing threats continue to go undetected. Keep Aware delivers real-time threat detection and prevention directly to the browser.
Le Lu
Chief Information Officer
One Workplace
“One persistent weak spot that has every organization faces is the browser, as existing solutions wrap around the browser but don’t effectively see what happens inside it. This browser visibility gap is critical stage of multi-step attacks on companies.
Michael Sutton
Former CISO
Zscaler
“The web browser is now a significant gap in visibility for security teams, and its central role in accessing online services and handling sensitive data makes it an attractive target for cybercriminals.
Ben Halpert
Former CISO
Groupon
“The human attack surface is most exposed through the web browser. Traditional security tools fail to cover this blind spot.
Jonathan Cran
Product and Engineering Leader
Google
“Protecting users has evolved to protecting them at the interfaces where they work. For many of us, the browser is where our most critical work takes place.
David Endler
Co-Founder
SpyCloud
“By understanding behavior within the browser, Keep Aware significantly enhances organizational security by revealing covert patterns, exposing elusive threats, and proactively safeguarding people and systems.
Greg Martin
CEO
Ghost Security
Why Keep Aware?
Proactive and Flexible Security
Against People-targeted Attacks
Real-time threat identification
at the point of click
Keep Aware embeds security directly into the web browser, protecting people where they work. Threats are identified and prevented in real time. 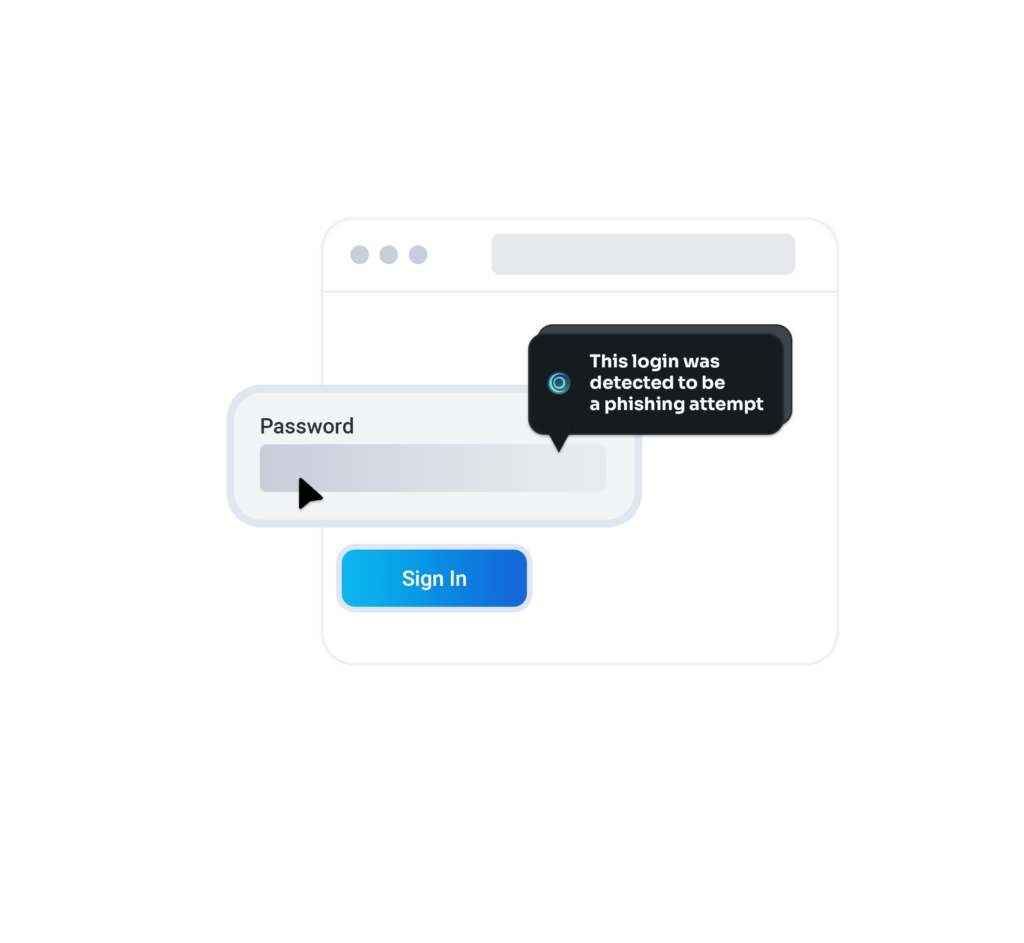
Native Protection from Known and Unknown Threats
Keep Aware provides robust security from attacks such as phishing, brand impersonation, social engineering and malicious extensions.Automated Investigations and Visibility
Keep Aware enables security teams to automatically triage incidents and report on human risk across the organization.

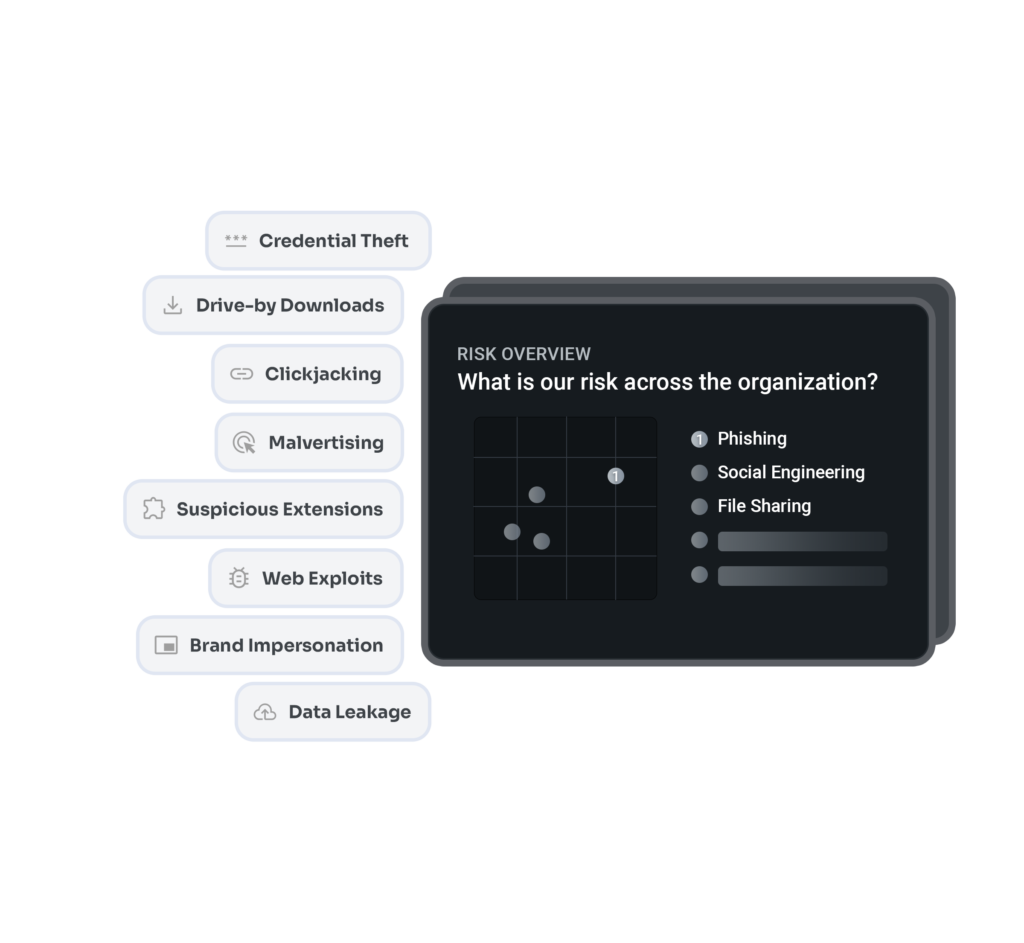
Direct deployment to the browsers you already use
Keep Aware is a non-disruptive and friction-less solution that integrates with an employee’s everyday workflow in minutes.Why Now?
Your Employees Spend up to 90% of their Day in a Web Browser Accessing Sensitive Systems and Data
That Browser is a Blind Spot to Perimeter-focused Security Solutions
Browser activity is a blind spot to traditional security solutions
Employees access sensitive data and SaaS applications via the browser
Bad actors have made the browser a primary attack vector
Existing controls block only known threats, novel threats prevail
Training is necessary but not sufficient, it is often forgotten
Employees continue to work outside the office, off the network
Employees work in several different browsers without central controls
Human error is the cause for the most severe data breaches
Artificial Intelligence has strengthened user-facing threats
